Highlights
- Security needs surrounding nuclear energy are evolving.
- Cybersecurity is an area of major concern in the power sector.
- A UT student is performing research that is gaining traction internationally.
As with many aspects of digital technology, I&C systems come with the need for cybersecurity measures that can keep nuclear reactors safe from malicious threats.
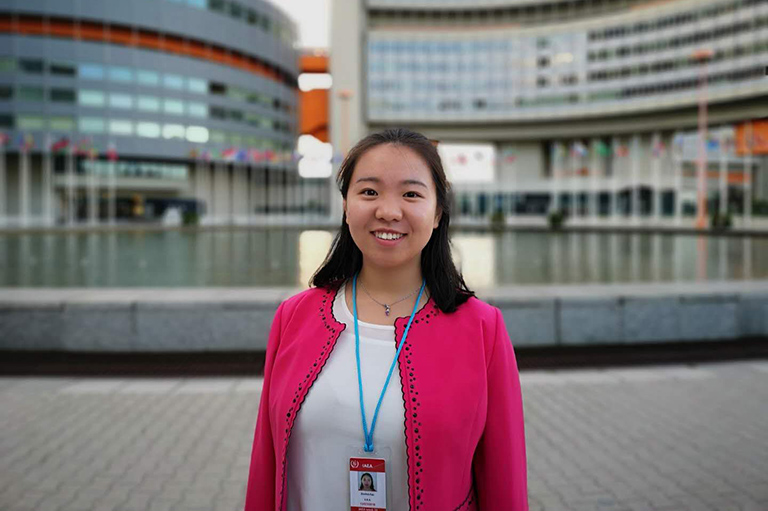
UT nuclear engineering doctoral student Fan Zhang is researching a new approach for enhancing cybersecurity within nuclear power plants, and her findings have found a home with one of the most respected bodies in the nuclear field—the International Atomic Energy Agency (IAEA).
—Fan Zhang
Zhang’s research involved first building a real-time cybersecurity test bed consisting of a simulated two-loop power system; a supervisory control and data acquisition (SCADA) system to receive data and pass control commands to the system; and a local area network to simulate cyber attacks.
Most current cybersecurity efforts use firewalls and network analysis to prevent attacks, but Zhang pointed out that threats originating from within, such as those coming from removable media and insiders still pose a risk despite such precautions. Additionally, data tampering attacks may not leave any trace in the actual networks themselves.
By using “process data” (data coming directly from the plant sensors) in combination with machine learning to detect when a cyberattack is ongoing or has occurred, on-site personnel would gain precious time to prevent severe damage, economic consequences, or potential loss of life.
The cybersecurity of nuclear power plants requires dedicated efforts to not only improve digital safeguards, but also to re-envision the way operational technology and information technology teams work. Zhang’s solution creates a novel architecture that promotes cross-collaboration by combining both teams.
The proposed cyber-attack detection system consists of three modules based on four types of data, including classification models, unsupervised models for process data, and network and host system data.
Zhang tested five types of attacks, including man in the middle (MITM), denial of service (DoS), data exfiltration, data tampering, and false data injection to simulate the consequences of a cyberattack and generate data for building data-driven detection models. The results show the proposed model is able to effectively detect these attacks carried out on the testbed with almost no false alarms.
A conversation with Michael T. Rowland, former IAEA cybersecurity director, led to Zhang being invited to participate in an IAEA Coordinated Research Project (CRP). This CRP, “Enhancing Computer Security Incident Response at Nuclear Facilities,” explores key areas such as best practices in cyberdefense; technology and analytical solutions for intrusion detection; and recommended procedures for response, including forensic activities for computer security incidents at nuclear facilities.
The CRP has led to Zhang sharing her research findings with partners from 17 institutes across 13 countries. She has presented her research at the CRP meetings in Canada, Austria, China, and South Korea as well as international conferences hosted by the American Nuclear Society and the International Society for Automation.
Her research will now be published and used in guidance and training of nuclear security methods for the IAEA. Additionally, this research has received substantial funding by the DoE’s Nuclear Energy University Program (NEUP) for a proposal entitled, “A Cyber-Attack Detection Platform for Cyber Security of Digital Instrumentation and Control Systems.” As one of the proposal’s co-authors, along with Assistant Professor and Southern Company Fellow Jamie Coble, Zhang has had a very strong influence on the direction and implementation of this project, which received an award of close to $800K in June.
In addition, this research was partially funded through Lloyd’s Register Foundation and the International Joint Research Center for the Safety of Nuclear Energy. Lloyd’s Register Foundation helps to protect life and property by supporting engineering-related education, public engagement, and the application of research.
Contact
Élan Young: elan@tennessee.edu